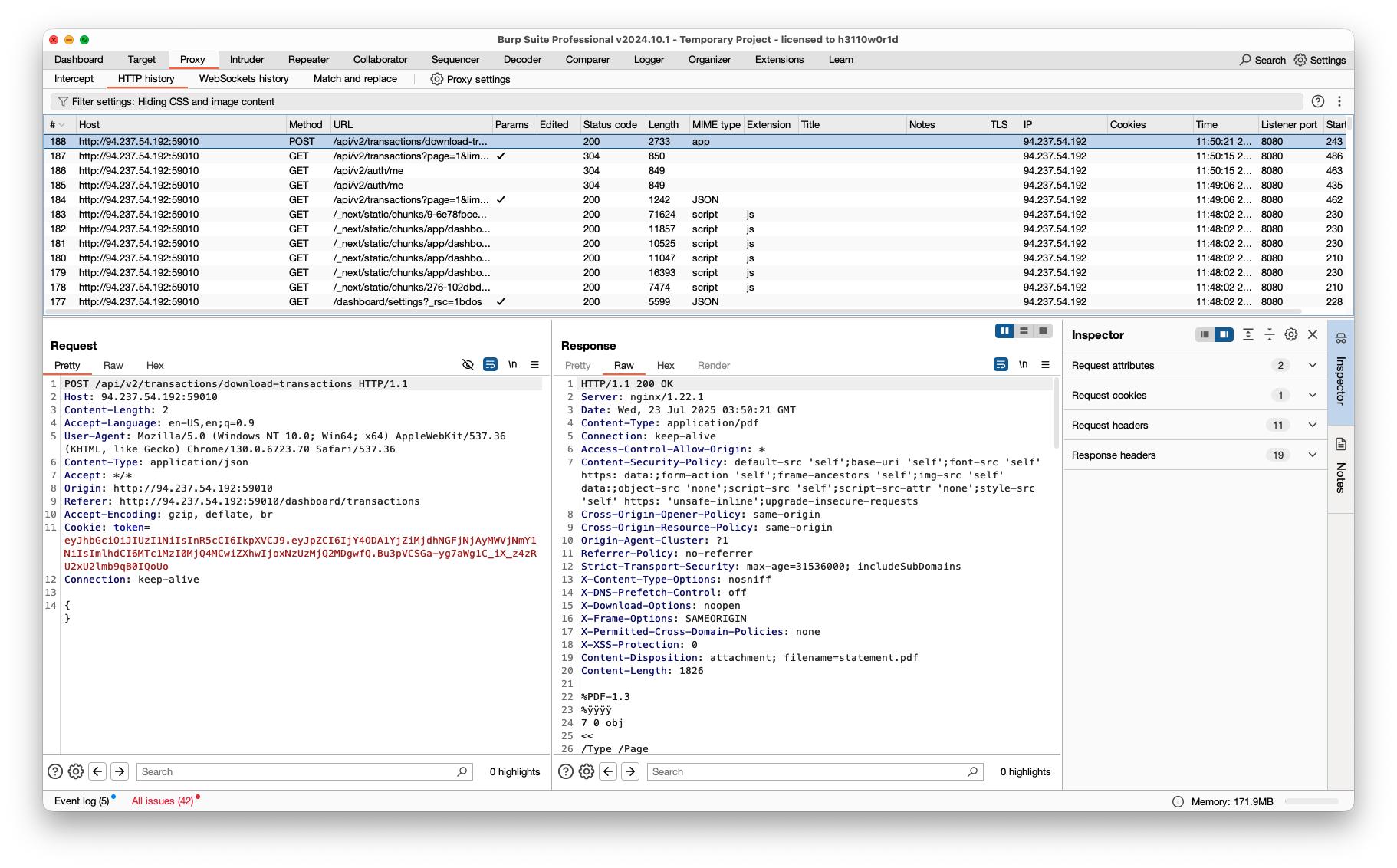
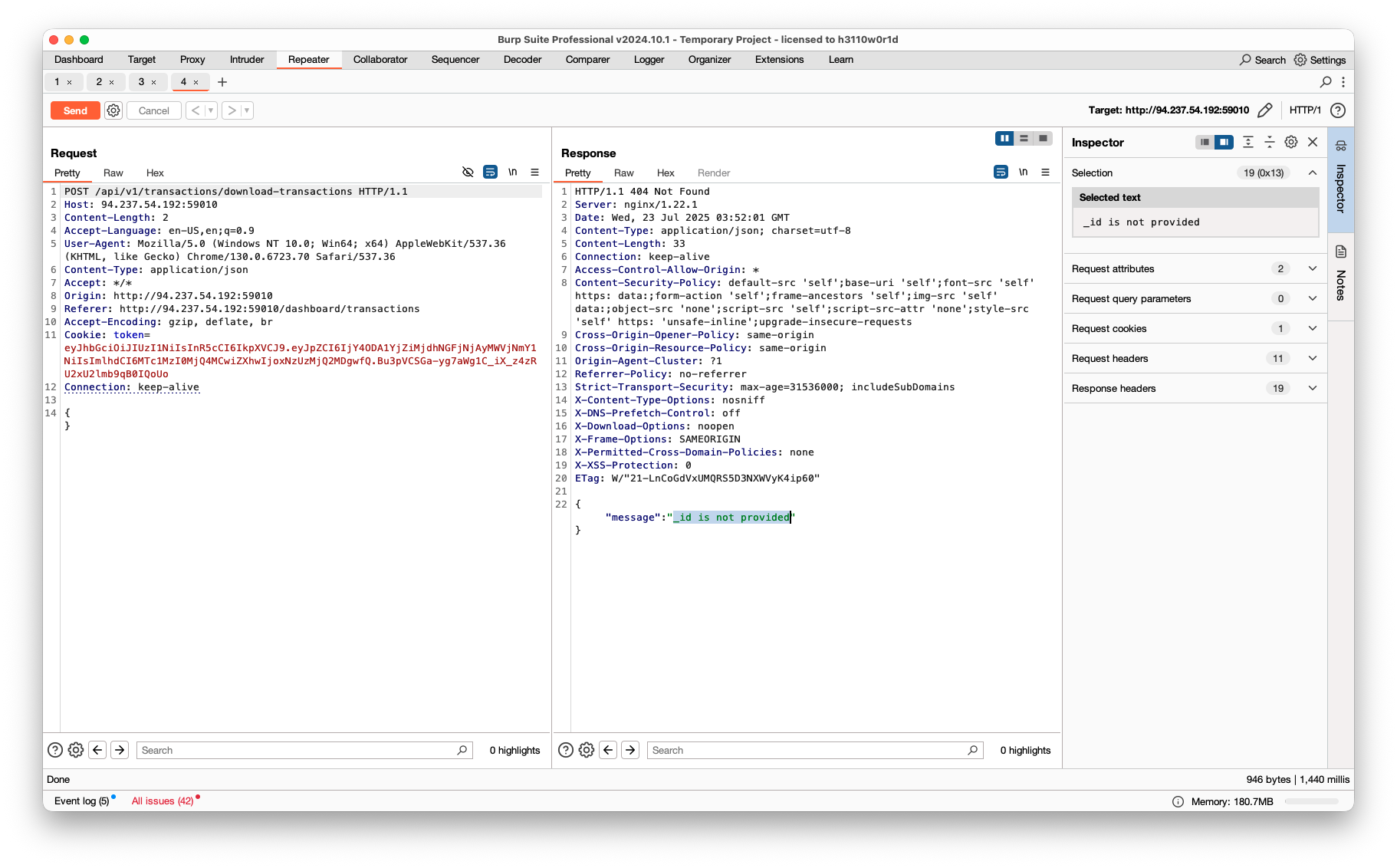
在数据包中可以看到所有的请求接口都是 v2 版本的,尝试使用 v1 版本的接口。
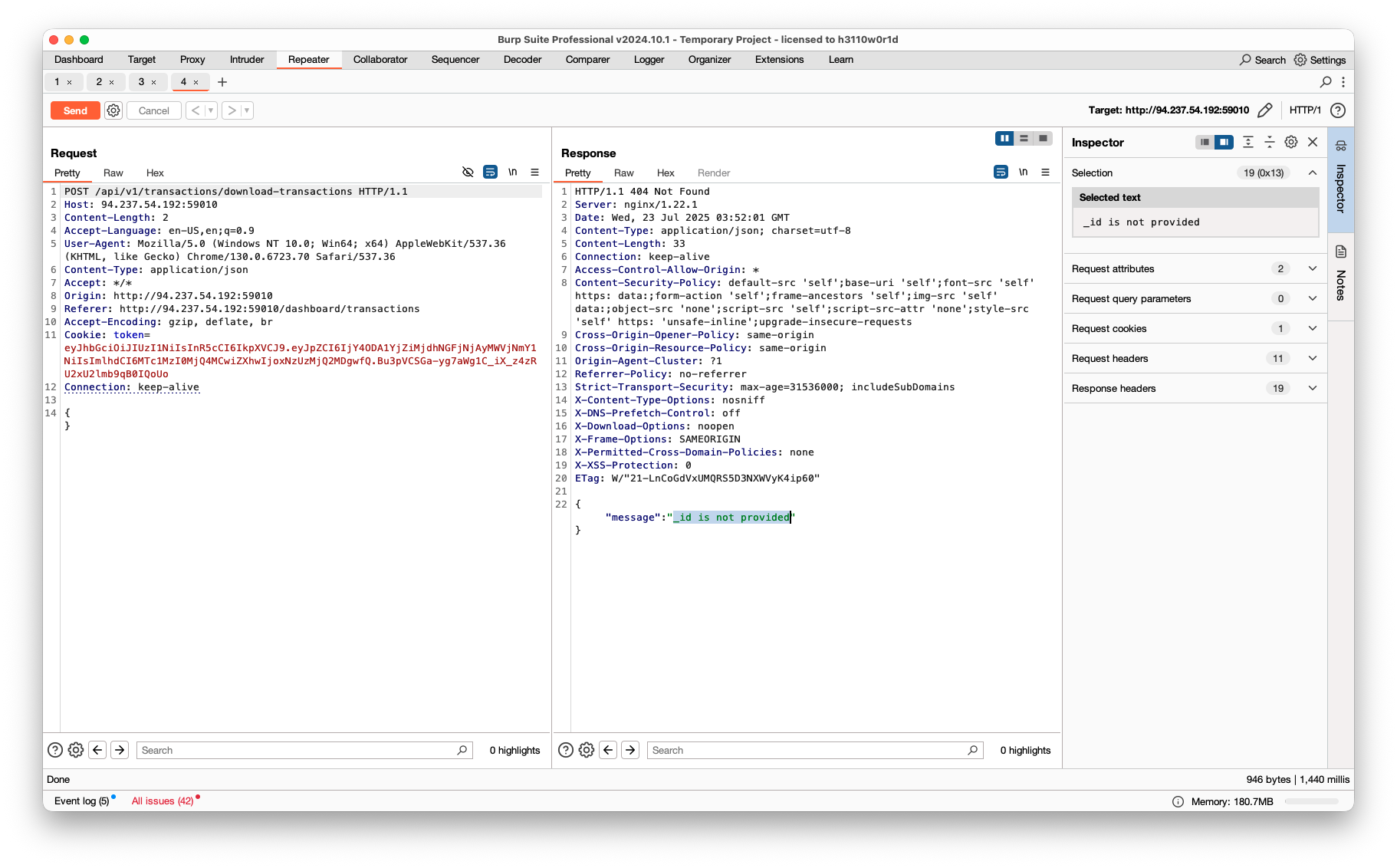
在下载交易PDF的接口时,使用 v1 版本的接口发现不需要使用JWT鉴权,而是使用 _id 作为参数。
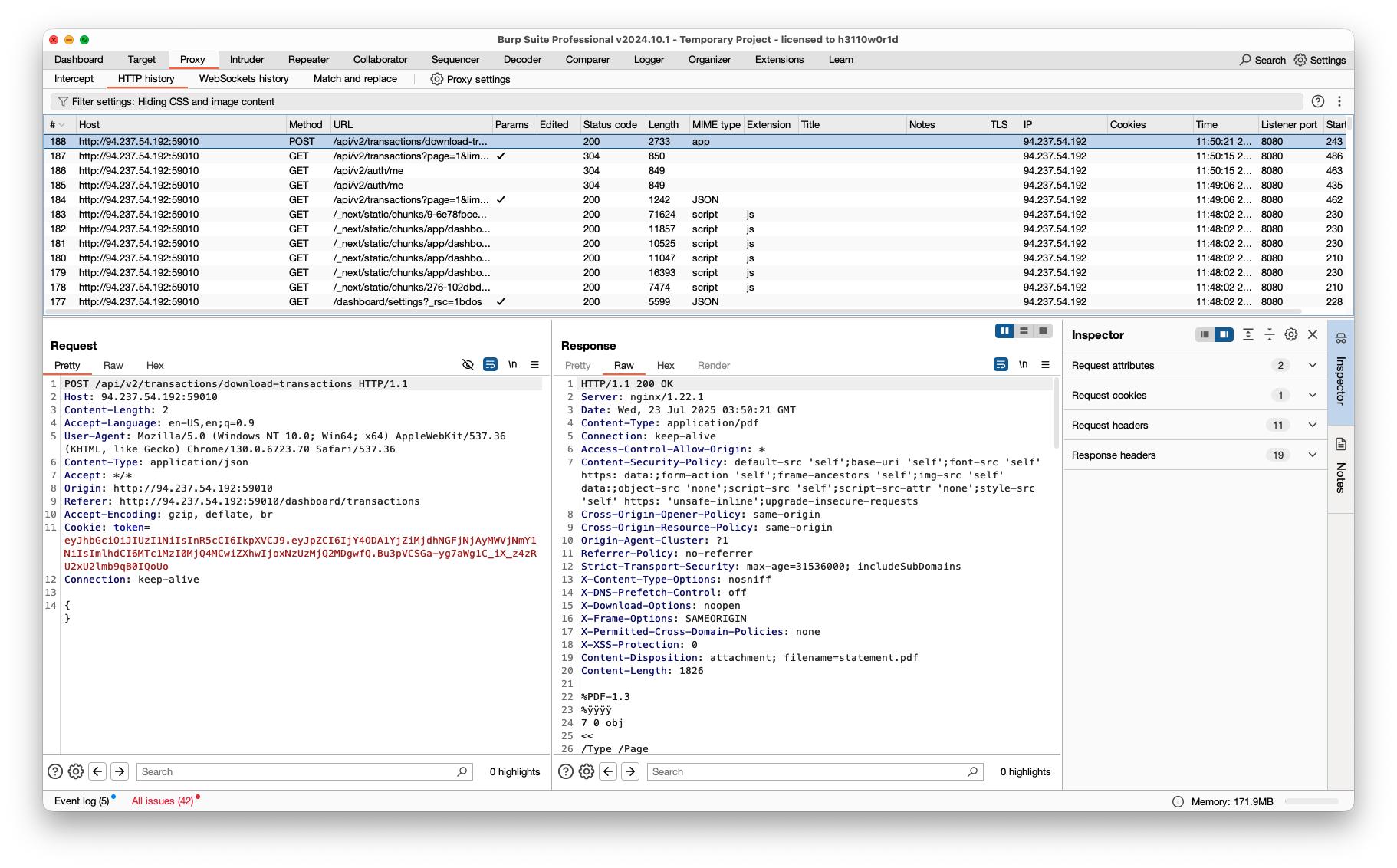
在数据包中可以看到所有的请求接口都是 v2 版本的,尝试使用 v1 版本的接口。
在下载交易PDF的接口时,使用 v1 版本的接口发现不需要使用JWT鉴权,而是使用 _id 作为参数。
简单的 cms,可以扫扫看?
提示 1: /flag.php:
if($_SERVER["REMOTE_ADDR"] != "127.0.0.1"){
echo "Just input 'cmd' From 127.0.0.1";
return;
}else{
system($\_GET['cmd']);
}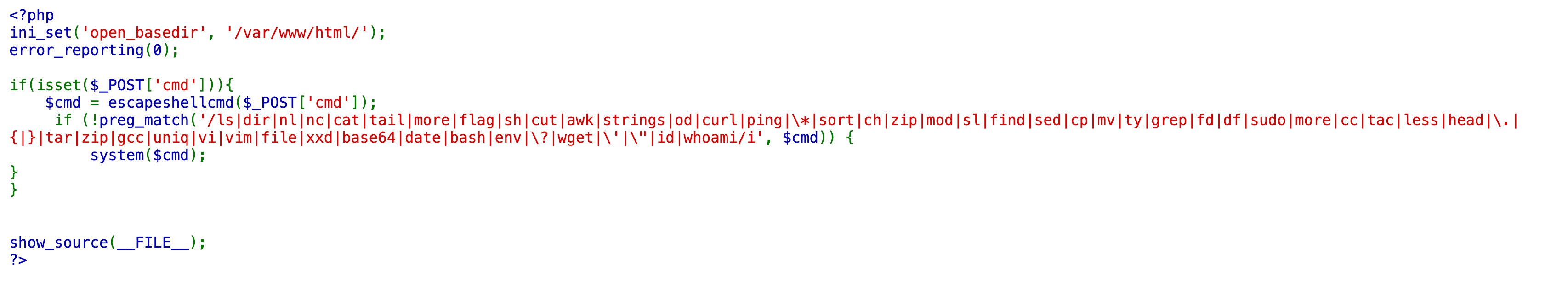
小明在学习 CTF 的过程中遇到了一道 PHP 的题目,以他有限的水平做不出来,可以帮帮他吗?
观察源码,只要我们传进去的 cmd 不被正则匹配到,就可以执行系统命令。
if(isset($_POST['cmd'])){
$cmd = escapeshellcmd($_POST['cmd']);
if (!preg_match('/ls|dir|nl|nc|cat|tail|more|flag|sh|cut|awk|strings|od|curl|ping|\*|sort|ch|zip|mod|sl|find|sed|cp|mv|ty|grep|fd|df|sudo|more|cc|tac|less|head|\.|{|}|tar|zip|gcc|uniq|vi|vim|file|xxd|base64|date|bash|env|\?|wget|\'|\"|id|whoami/i', $cmd)) {
system($cmd);
}
}
Someone said: 'One advantage of having a homemade server is that it becomes much harder to hack.' Do you agree? Give reasons.
Note: The files in src/public are unrelated for the challenge.
Chilli Level:

"A QA engineer walks into a bar. Orders a beer. Orders 0 beers. Orders 99999999999 beers. Orders a lizard. Orders -1 beers. Orders a ueicbksjdhd."
I am working on yet another CTF platform. I haven't implement all the features yet, but I am confident that it is at least secure.
Thanks to Poe I coded a webpage to PDF in seconds! I am genius right?
Chilli Level:
点击页面中的所有按钮,发现整个网站只有登录和注册两个功能,所以我们在源码中关注这两个功能。
在源码中全局搜索 flag 后,在 ProfileController 中发现了读取 flag 的代码。
public function index() {
$token = (string) $_COOKIE["token"] ?? null;
$flag = file_get_contents(filename: APPPATH . "/../flag.txt");
if (isset($token)) {
$key = (string) getenv("JWT_SECRET");
$jwt_decode = JWT::decode($token, new Key($key, "HS256"));
$username = $jwt_decode->username;
if ($username == "administrator") {
return view("ProfilePage", [
"username" => $username,
"content" => $flag,
]);
} else {
$content = "Haven't seen you for a while";
return view("ProfilePage", [
"username" => $username,
"content" => $content,
]);
}
}
}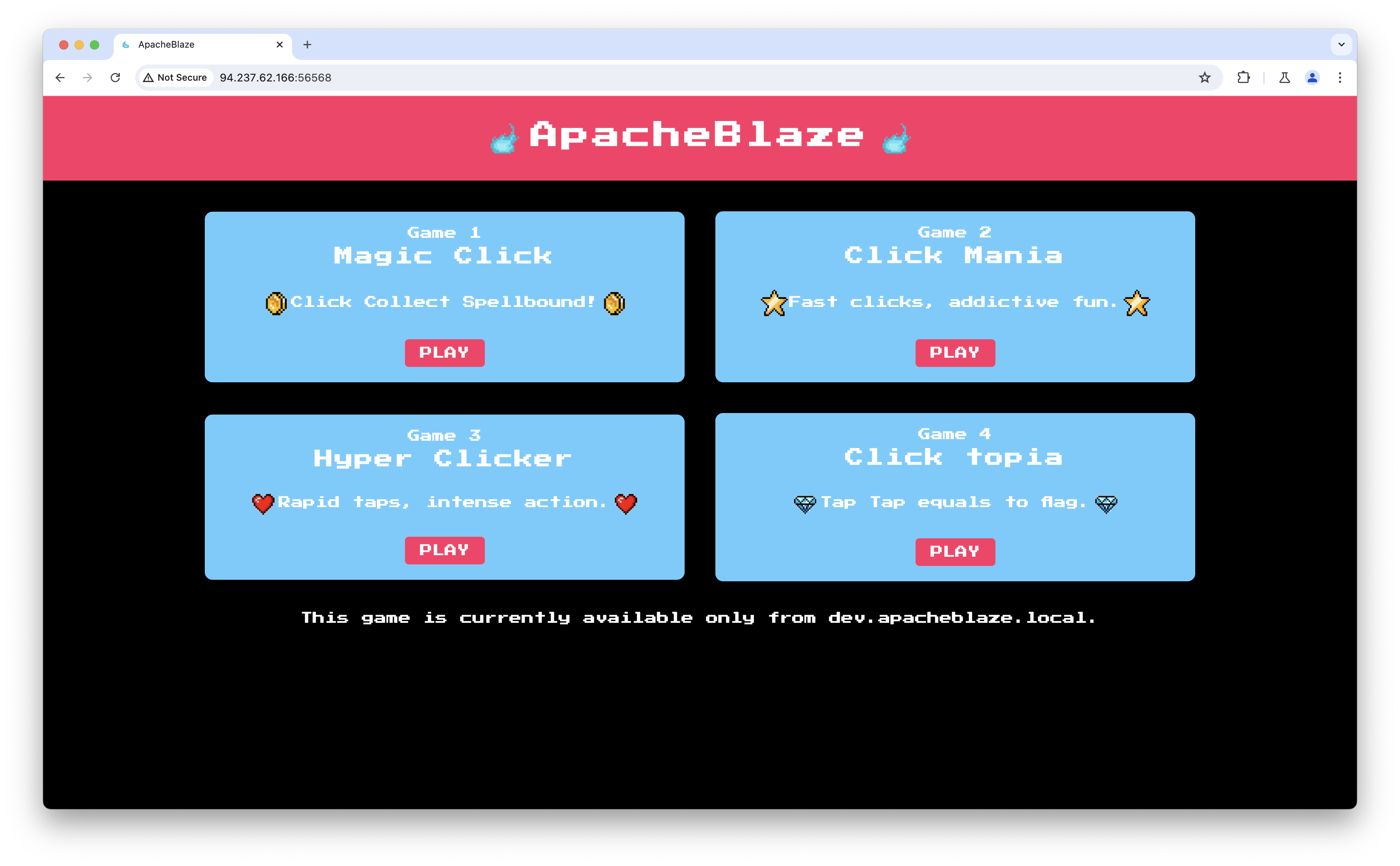
点击页面的按钮后发现提示 This game is currently available only from dev.apacheblaze.local.
在源码中搜索这个域名,找到对应处理函数
@app.route('/', methods=['GET'])
def index():
game = request.args.get('game')
if not game:
return jsonify({
'error': 'Empty game name is not supported!.'
}), 400
elif game not in app.config['GAMES']:
return jsonify({
'error': 'Invalid game name!'
}), 400
elif game == 'click_topia':
print(request.headers)
if request.headers.get('X-Forwarded-Host') == 'dev.apacheblaze.local':
return jsonify({
'message': f'{app.config["FLAG"]}'
}), 200
else:
return jsonify({
'message': 'This game is currently available only from dev.apacheblaze.local.'
}), 200
else:
return jsonify({
'message': 'This game is currently unavailable due to internal maintenance.'
}), 200
观察 game.js 源码
if (data.status === "game_over") {
alert(`Game Over! Your score: ${data.score}`);
reset_game();
} else if (data.status === "win") {
window.location.href = `${data.url}`;
} else {
snake = data.snake;
food = { x: data.food[0], y: data.food[1] };
score = data.score;
draw();
}